The global cybersecurity landscape in 2026 presents a startling irony where organizations possess more sophisticated defensive tools than ever before, yet they remain fundamentally ill-equipped to handle the chaotic reality of a live, large-scale breach. This profound disconnect between theoretical preparation and operational performance has created a pervasive “readiness gap,” a phenomenon where documented security strategies fail to translate into effective defensive actions during high-stakes incidents. Recent findings indicate that while approximately 99 percent of organizations have a formalized incident response plan, nearly three-quarters of senior security leaders admit their firms would not be fully ready to withstand a significant attack hitting tomorrow. This lack of confidence highlights a transition from a state of actual security to one of “paper compliance,” where plans are drafted to satisfy regulatory checklists rather than to ensure survival under duress. When a major exploit occurs, the theoretical structures often crumble, revealing that many organizations are operating under a false sense of security that prioritizes the existence of a manual over the ability to execute its contents under extreme pressure.
Building on this systemic vulnerability, the “readiness gap” suggests that the current focus on policy creation has not been matched by a commitment to operational testing or resource allocation. The mere existence of a response document does not equate to the proficiency of the team tasked with using it, especially when fewer than 40 percent of decision-makers describe their core defensive functions—such as digital forensics or threat hunting—as being highly effective. This suggests that the security industry is currently struggling with a crisis of execution, where the technical skills and procedural workflows required to mitigate a breach are not keeping pace with the evolving sophistication of threat actors. As a result, the transition from a passive defensive posture to an active response phase remains the most significant point of failure for contemporary enterprises. This lack of agility not only extends the duration of an incident but also exponentially increases the financial and operational fallout that follows the initial compromise.
The Disconnect Between Policy and Performance
The prevalence of “paper compliance” has created a dangerous environment where organizations believe they are protected because they have checked the necessary boxes for internal audits and external regulations. While 99 percent of surveyed firms maintain documented incident response plans, the admission by 73 percent of leaders that they are unready for an immediate attack underscores a massive failure in practical application. This discrepancy is often rooted in the fact that these plans are frequently static documents that do not account for the dynamic, non-linear nature of modern cyber warfare. When a security team is forced to respond to a zero-day exploit or a multi-stage ransomware attack, they often find that the predefined steps in their manual are too rigid or lack the granularity required to address specific technical nuances. Consequently, the reliance on outdated or untested protocols leads to a state of paralysis during the critical first hours of an incident, allowing attackers to deepen their foothold within the corporate network.
The urgency of this situation is further punctuated by the sheer volume and severity of attacks that have characterized the current year. Data reveals that 76 percent of organizations faced at least one significant cyber attack within the last twelve months, with nearly a third being targeted multiple times. These are not merely digital inconveniences; they result in catastrophic consequences, including total operational shutdowns for 47 percent of victims and significant data loss for 41 percent. In sectors like decentralized finance and cryptocurrency, where 83 percent of firms have reported being targeted, the stakes are even higher due to the immediate liquidity of assets. Similarly, the retail and manufacturing sectors face immense pressure because their business models rely on continuous uptime and supply chain integrity. For these industries, any delay in response translates directly into millions of dollars in lost revenue and a long-term erosion of consumer trust that can take years to rebuild after the initial breach.
Internal Friction and the Leadership Vacuum
A primary obstacle to effective incident response is not always found in the technical stack, but rather in the deep-seated organizational friction that occurs when multiple stakeholders must coordinate under pressure. Approximately 90 percent of security leaders anticipate significant difficulty in aligning various departments—such as IT, legal, human resources, and communications—during a live crisis. This coordination breakdown is often the result of siloed operations where the security team works in isolation from the rest of the business until a disaster occurs. Without pre-established communication channels and a clear understanding of roles and responsibilities, the initial response to an attack is often characterized by confusion and conflicting priorities. This internal chaos provides threat actors with the “dwell time” they need to exfiltrate sensitive data or deploy more damaging payloads while the organization is still debating its internal chain of command.
This lack of cohesion is exacerbated by a significant “executive gap,” where senior leadership and board members remain largely disconnected from the technical realities of cybersecurity readiness. Nearly 89 percent of security leaders report that limited involvement from the C-suite is a major hurdle, as it creates a vacuum of authority during critical decision-making moments. When the board of directors is not integrated into regular readiness exercises or tabletop simulations, they are often unprepared to provide the rapid approvals needed for aggressive mitigation strategies. Furthermore, 75 percent of respondents noted that legal and communications teams often introduce delays that hinder the speed of the technical response. In the private healthcare sector, this concern is even more acute, with 86 percent of leaders identifying legal bottlenecks as a primary obstacle. The high regulatory stakes of patient data privacy often lead to a cautious, slow-moving approach that is fundamentally at odds with the rapid pace required to contain a modern cyber threat.
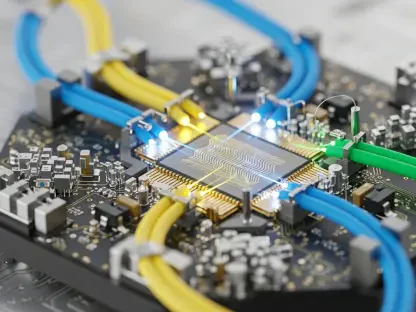
Technological Blind Spots and the Impact of New Tech
Maintaining comprehensive visibility across a modern enterprise has become an increasingly difficult task as infrastructure becomes more decentralized and complex. Seventy-eight percent of security professionals acknowledge that critical visibility gaps exist within their environments, creating “blind spots” where attackers can operate without detection for extended periods. These gaps are prevalent across public cloud environments, SaaS platforms, and traditional on-premises systems, with nearly 90 percent of organizations reporting some level of opacity in each area. When security teams cannot see every corner of their network, they cannot reliably detect lateral movement or unauthorized data access, which often leads to repeat incidents where the same attacker returns after a supposed remediation. This lack of clarity forces organizations into a reactive cycle, where they are constantly chasing threats they only partially understand rather than proactively securing their most sensitive assets.
The convergence of corporate IT systems with Operational Technology and Industrial Control Systems has introduced a new dimension of risk that many organizations are not prepared to manage. Eighty-four percent of respondents expressed deep concern regarding the potential for attackers to pivot from office-based networks into the systems that control physical production lines and critical infrastructure. As these environments become more integrated to support digital transformation goals, the potential for physical disruption—such as halting a factory or compromising a power grid—increases significantly. Furthermore, while 63 percent of organizations plan to embed artificial intelligence into their threat detection and response activities by next year, this technology is not a universal solution. AI can certainly scale detection efforts and improve triage speed, but it also represents an expanding attack surface. If AI tools are deployed without rigorous security governance, they can be manipulated by adversaries to bypass traditional defenses, creating a new class of vulnerabilities that require specialized expertise to address.
Realigning Investments for True Resilience
In response to the pervasive lack of confidence in existing defenses, many organizations have begun to fundamentally shift how they allocate their security budgets and manage their external partnerships. The current trend emphasizes a move away from static, perimeter-based security toward a more dynamic model focused on continuous monitoring and proactive threat detection. Eighty-five percent of firms are now prioritizing investments in 24/7 continuous threat monitoring, while 81 percent are seeking broader Managed Detection and Response coverage to fill internal talent gaps. This shift reflects a growing realization that preventing every attack is impossible, making the ability to detect and contain a breach the most critical metric of success. Additionally, there has been a significant rise in the adoption of simulation exercises and red-teaming, as 75 percent of leaders recognize that theoretical plans must be stress-tested against realistic attack scenarios to identify hidden weaknesses.
This widespread dissatisfaction with current readiness levels has also led to a high rate of provider churn, with 65 percent of organizations indicating they will likely switch their incident response providers when their current contracts expire. Leaders are increasingly seeking partners who offer a “vendor-agnostic” approach and can provide deep expertise across diverse environments, including cloud, IT, and OT systems. The move toward more specialized and proactive support suggested that the industry was finally moving past the era of generic security services. Organizations eventually realized that true resilience required a holistic strategy that combined advanced technology with cross-functional governance and regular, board-level engagement. By prioritizing the elimination of visibility gaps and fostering a culture of continuous testing, forward-thinking enterprises took the necessary steps to ensure they were part of the minority capable of surviving a major cyber event without suffering catastrophic operational failure. These proactive measures ultimately transformed cybersecurity from a technical checkbox into a core pillar of organizational durability.